Rootkit Ntoskrnl Exercises
State-of-the-Art algorithms for rootkit detection are pre- sented in this paper. Forensic techniques to monitor the. Outside the memory image of ntoskrnl.exe (for SSDT) or win32k.sys (for Shadow SSDT). The driver exercises complex inner workings of a chip and checks for correct responses.
Uroburos was already described as a very sophisticated and highly complex malware in our G DATA Red Paper, where we had a look at the malware’s behavior. This malware belongs to a specific type called rootkit. The general purpose of a rootkit is to modify the behavior of the system and, especially, to hide its activity. Generally, a rootkit resides in the kernel. To analyze this kind of malicious software, analysts need to use specific tools, such as WinDbg, to debug the Microsoft Windows kernel.
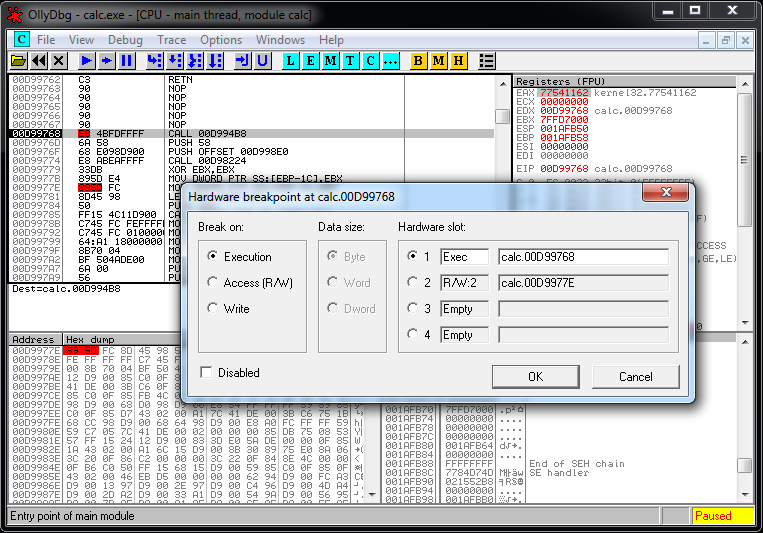
WinDbg is a debugger provided by Microsoft. One can use this tool to debug user mode applications and kernel mode applications (for example the drivers).
Today, we would like to give you an understanding of how analysts work their way through malware and give you some insights into the code of one of the most sophisticated digital threats. In this current example case, we decided to work with a memory dump (crash dump) of a system infected with Uroburos. To facilitate the analysis, we added an extension to add the support of python, called: PyKd. WinDbg has its own script language, but it is not easy to understand. One can download this python extension here, for free: To realize this article, the machine was infected by the Uroburos dropper with the following md5: 626576e5f0f85d77c460a322a92bb267.
Visualization of the hooks The Uroburos rootkit adds several hooks to hide its activity. In our specific case, the hooking is a technique used to alter the behavior of specific system functions; the rootkit fakes the output of the Microsoft Windows API. For example, it hides registry entries, files and more. To perform this task, the rootkit developers decided to use interrupts. We can display the Interrupt Descriptor Table (IDT), as shown below. The IDT table stores pointers to ISR (Interrupt Service Routines), which are called when an interrupt is triggered.
This output shows us two remarkable things: • First, the driver uses a well-known Windows kernel memory pool tag called 'NtFs'. The Windows components mark allocated memory block with a unique tag. But the rootkit uses the same tag as the legitimate ntfs.sys driver. This choice was made to hide the rootkit and dupe the analyst. • Secondly, the output looks like the beginning of a PE. But this PE is broken: the MZ is not available and some information is missing. Download Berlitz English Course more.
For example, the value of the SizeOfImage (85980000+0x140) is null. Warriors Orochi 3 Keygen Idm on this page. The rootkit alters the beginning of the PE to hide itself. Some tools parse the memory and look for the MZ string to identify the beginning of a PE.
In our current case, if we used these tools looking for a PE file, we would never identify our malware using this automation. Manual analysis is needed here. To dump our driver we need to reconstruct the PE but we don't know the size of the binary, as mentioned above, so we need to make a large dump, to be sure to not forget a part of the binary.
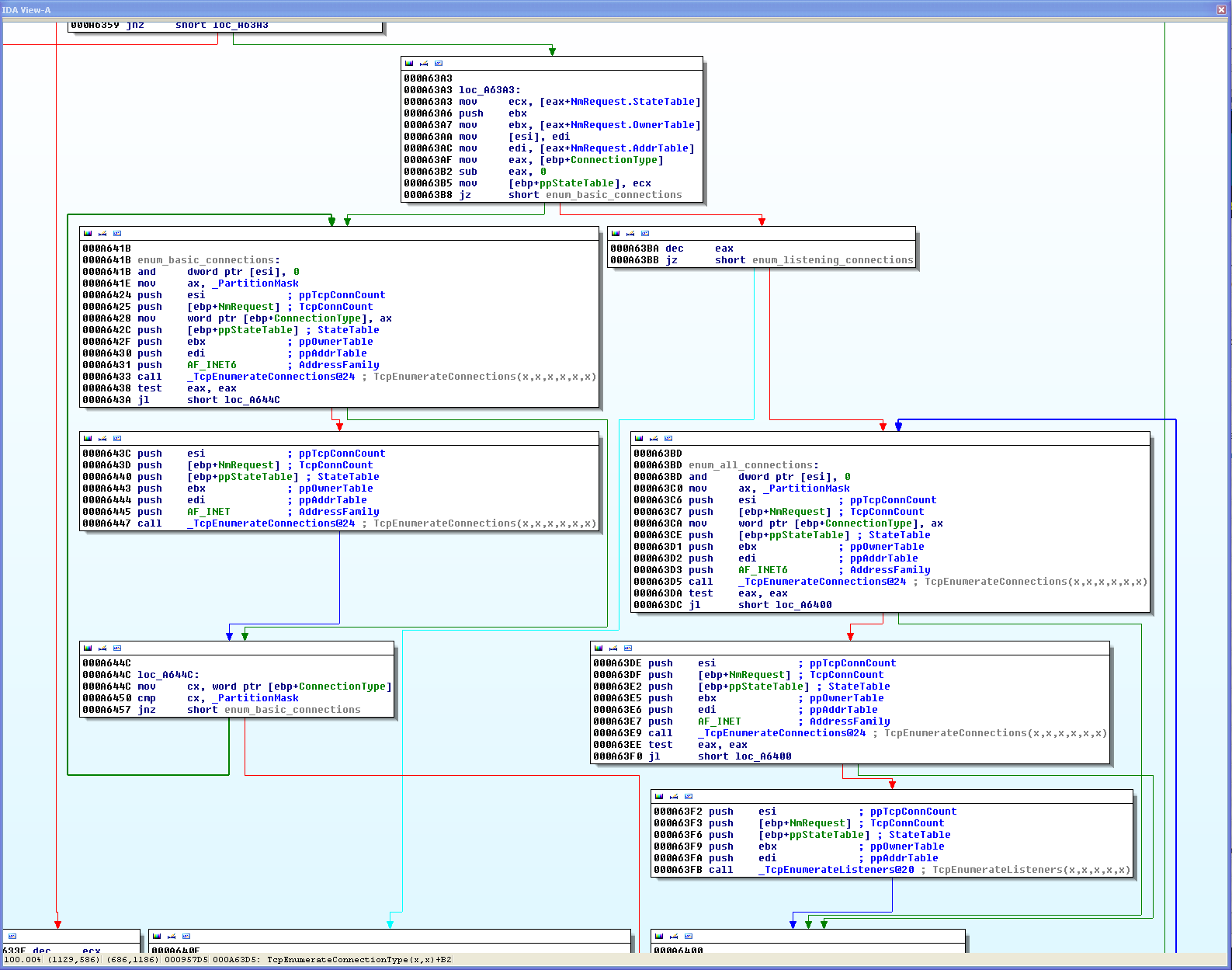
Modules, drivers and devices We can now display the loaded (and unloaded) modules with WinDbg. Two objects are particularly interesting: FWPMCALLOUT and RawDisk1 WFP callout This first device is FWPMCALLOUT. Thanks to the name of the device we can guess that the rootkit registers a callout for Windows Filtering Platform (WFP). The WFP is a set of API and system services which provides a platform for creating network filtering applications. Check Sc Drivers License Status on this page.





